Row Internet Marketing : Menghadirkan Inovasi dalam Pemasaran Online
Pemasaran online (internet marketing) telah menjadi salah satu strategi yang tak terelakkan dalam dunia bisnis saat ini. Dengan semakin berkembangnya teknologi dan penggunaan internet yang semakin meluas, peluang untuk memasarkan produk atau jasa secara online semakin besar. Namun, seiring dengan banyaknya bisnis yang berlomba-lomba memanfaatkan pemasaran online, persaingan semakin ketat dan membuat pelaku bisnis harus terus berinovasi untuk tetap relevan dan menarik minat konsumen.
Dalam menghadapi situasi yang semakin kompetitif ini, Row Internet Marketing hadir sebagai solusi untuk membantu pelaku bisnis meningkatkan kehadiran dan daya saingnya di dunia maya. Row Internet Marketing merupakan sebuah situs oleh Jasa Website Murah yang berfokus pada pemasaran online dan memberikan layanan yang komprehensif untuk membantu pelaku bisnis mempromosikan produk atau jasa mereka secara efektif.
Salah satu inovasi yang ditawarkan oleh Row Internet Marketing adalah penggunaan teknologi artificial intelligence (AI) dalam strategi pemasaran online. Dengan menggabungkan AI dan analisis data yang akurat, www.row.im mampu mengidentifikasi target pasar yang tepat dan mengoptimalkan kampanye pemasaran yang sesuai dengan karakteristik dan perilaku konsumen. Hal ini membuat proses pemasaran menjadi lebih efisien dan efektif, serta memberikan hasil yang lebih maksimal.
Selain itu, Row Internet Marketing juga menawarkan layanan pembuatan konten yang kreatif dan menarik untuk memberikan daya tarik tersendiri bagi produk atau jasa yang dipromosikan. Konten yang unik dan menarik akan membuat konsumen tertarik untuk memperhatikan dan mengingat produk atau jasa yang ditawarkan, sehingga meningkatkan peluang untuk mendapatkan konversi penjualan.
Tidak hanya itu, https://row.im/ juga menawarkan layanan manajemen media sosial yang dapat membantu pelaku bisnis meningkatkan kehadiran dan interaksi di berbagai platform media sosial. Dengan memanfaatkan media sosial yang tepat dan strategi yang efektif, Row Internet Marketing membantu membangun brand awareness dan memperluas jangkauan pasar dari produk atau jasa yang dipromosikan.
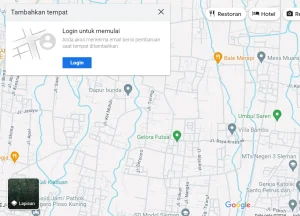
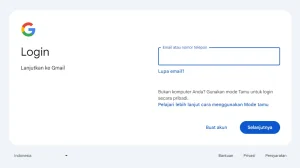
Tak hanya berfokus pada pemasaran online,Row Internet Marketing juga memberikan perhatian pada pengembangan website yang responsif dan user-friendly. Hal ini memungkinkan konsumen untuk dengan mudah menemukan informasi yang mereka butuhkan dan membuat pengalaman berbelanja menjadi lebih menyenangkan dan nyaman. Selain itu, Row Internet Marketing juga menawarkan layanan hosting murah yang dapat dimanfaatkan oleh para pelaku bisnis untuk memunculkan bisnis mereka di internet, sehingga memudahkan konsumen untuk menemukan produk atau jasa yang mereka tawarkan secara online.
Dengan menghadirkan berbagai inovasi dalam pemasaran online, Row Internet Marketing telah membantu banyak pelaku bisnis untuk memperluas dan meningkatkan kehadiran mereka di dunia maya. Dengan komitmen untuk terus berinovasi dan memberikan layanan yang berkualitas, Row Internet Marketing mampu menjadi mitra yang andal dalam meningkatkan daya saing dan kesuksesan bisnis secara online. Jadi, bagi pelaku bisnis yang ingin meningkatkan kehadiran dan penjualan secara online, Row Internet Marketing adalah pilihan yang tepat.